Kubernetes Auth is a Kubernetes-native authentication method for applications (e.g. pods) to access Infisical.Documentation Index
Fetch the complete documentation index at: https://infisical.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
Diagram
The following sequence diagram illustrates the Kubernetes Auth workflow for authenticating applications running in pods with Infisical.Concept
At a high-level, Infisical authenticates an application in Kubernetes by verifying its identity and checking that it meets specific requirements (e.g. it is bound to an allowed service account) at the/api/v1/auth/kubernetes-auth/login endpoint. If successful,
then Infisical returns a short-lived access token that can be used to make authenticated requests to the Infisical API.
To be more specific:
- The application deployed on Kubernetes retrieves its service account credential that is a JWT token at the
/var/run/secrets/kubernetes.io/serviceaccount/tokenpod path. - The application sends the JWT token to Infisical at the
/api/v1/auth/kubernetes-auth/loginendpoint after which Infisical forwards the JWT token to the Kubernetes API Server at the TokenReview API for verification and to obtain the service account information associated with the JWT token. Infisical is able to authenticate and interact with the TokenReview API by using either the long lived JWT token set while configuring this authentication method or by using the incoming token itself. The JWT token mentioned in this context is referred as the token reviewer JWT token. - Infisical checks the service account properties against set criteria such Allowed Service Account Names and Allowed Namespaces.
- If all is well, Infisical returns a short-lived access token that the application can use to make authenticated requests to the Infisical API.
Guide
In the following steps, we explore how to create and use identities for your applications in Kubernetes to access the Infisical API using the Kubernetes Auth authentication method.Obtaining the token reviewer JWT for Infisical
Option 1: Reviewer JWT Token
Option 1: Reviewer JWT Token
system:auth-delegator cluster role. As described here, this role allows delegated authentication and authorization checks, specifically for Infisical to access the TokenReview API. You can apply the following configuration file:Secret resource:Option 2: Client JWT as Reviewer JWT Token
Option 2: Client JWT as Reviewer JWT Token
system:auth-delegator role:Option 3: Use Gateway as Reviewer
Option 3: Use Gateway as Reviewer
system:auth-delegator ClusterRole binding.Deploying a gateway
Grant the gateway the system:auth-delegator ClusterRole binding
system:auth-delegator ClusterRole binding, you can use the following command:Configure the Kubernetes Auth authentication method for the identity
Review Method to “Gateway as Reviewer”, and select the gateway you want to use as the token reviewer.You can select either an individual gateway or a Gateway Pool for automatic failover. When a pool is selected, the platform routes through a healthy gateway at request time. See Gateway Pools for more details.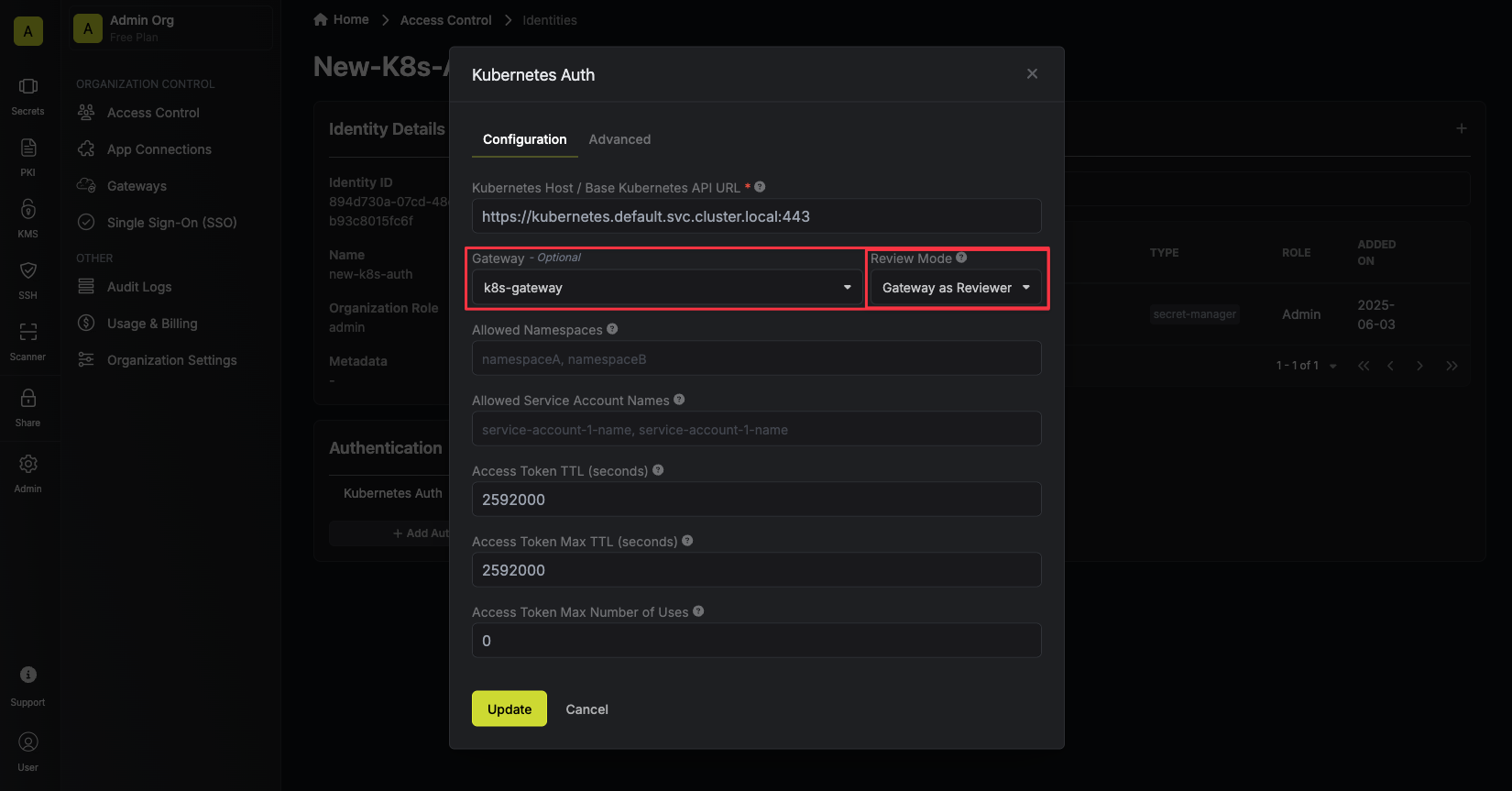
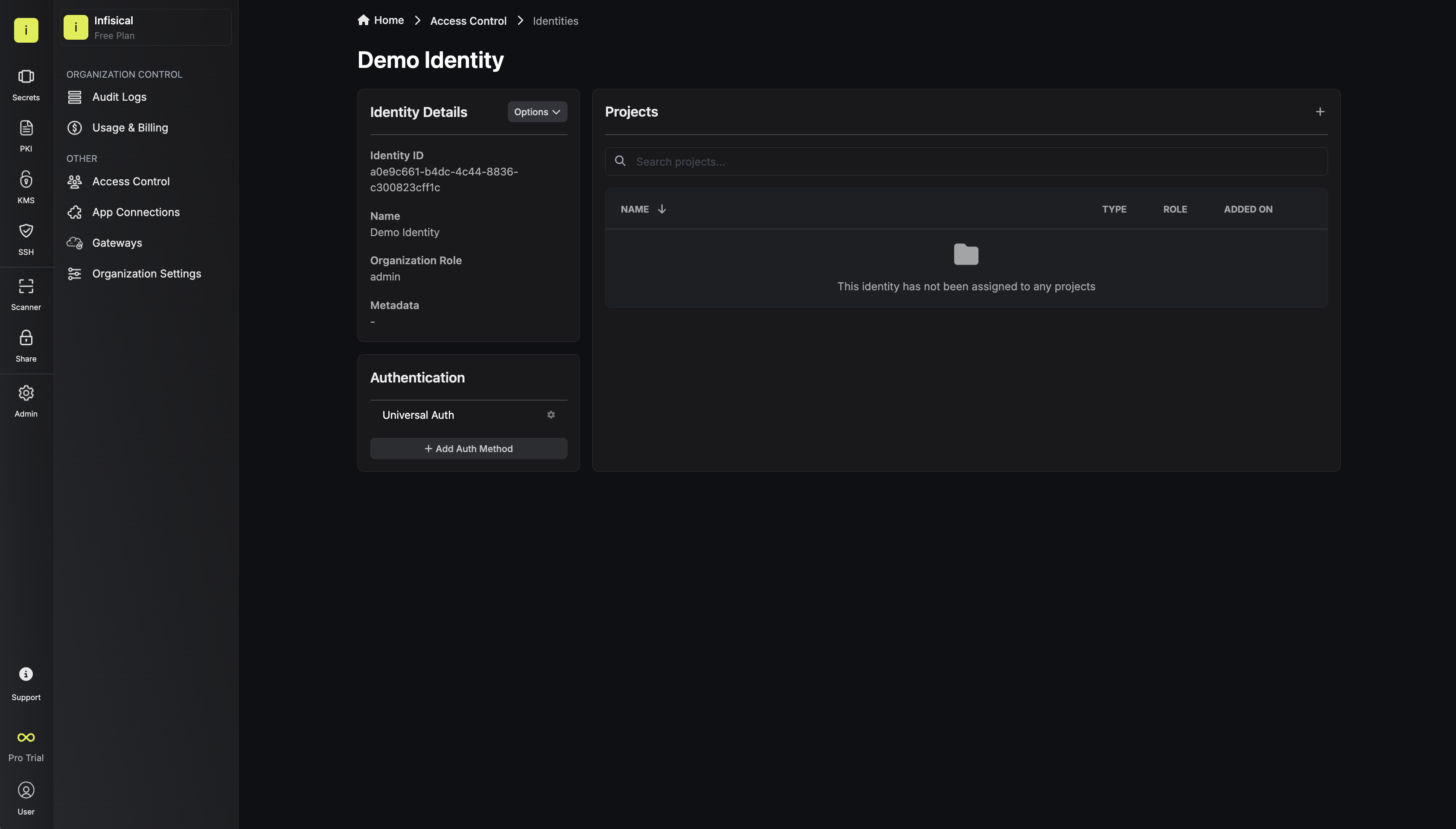
Creating an identity
 When creating an identity, you specify an organization level role for it to assume; you can configure roles in Organization Settings > Access Control > Organization Roles.
When creating an identity, you specify an organization level role for it to assume; you can configure roles in Organization Settings > Access Control > Organization Roles. Now input a few details for your new identity. Here’s some guidance for each field:
Now input a few details for your new identity. Here’s some guidance for each field:- Name (required): A friendly name for the identity.
- Role (required): A role from the Organization Roles tab for the identity to assume. The organization role assigned will determine what organization level resources this identity can have access to.
 Since the identity has been configured with Universal Auth by default, you should re-configure it to use Kubernetes Auth instead. To do this, press to edit the Authentication section,
remove the existing Universal Auth configuration, and add a new Kubernetes Auth configuration onto the identity.
Since the identity has been configured with Universal Auth by default, you should re-configure it to use Kubernetes Auth instead. To do this, press to edit the Authentication section,
remove the existing Universal Auth configuration, and add a new Kubernetes Auth configuration onto the identity.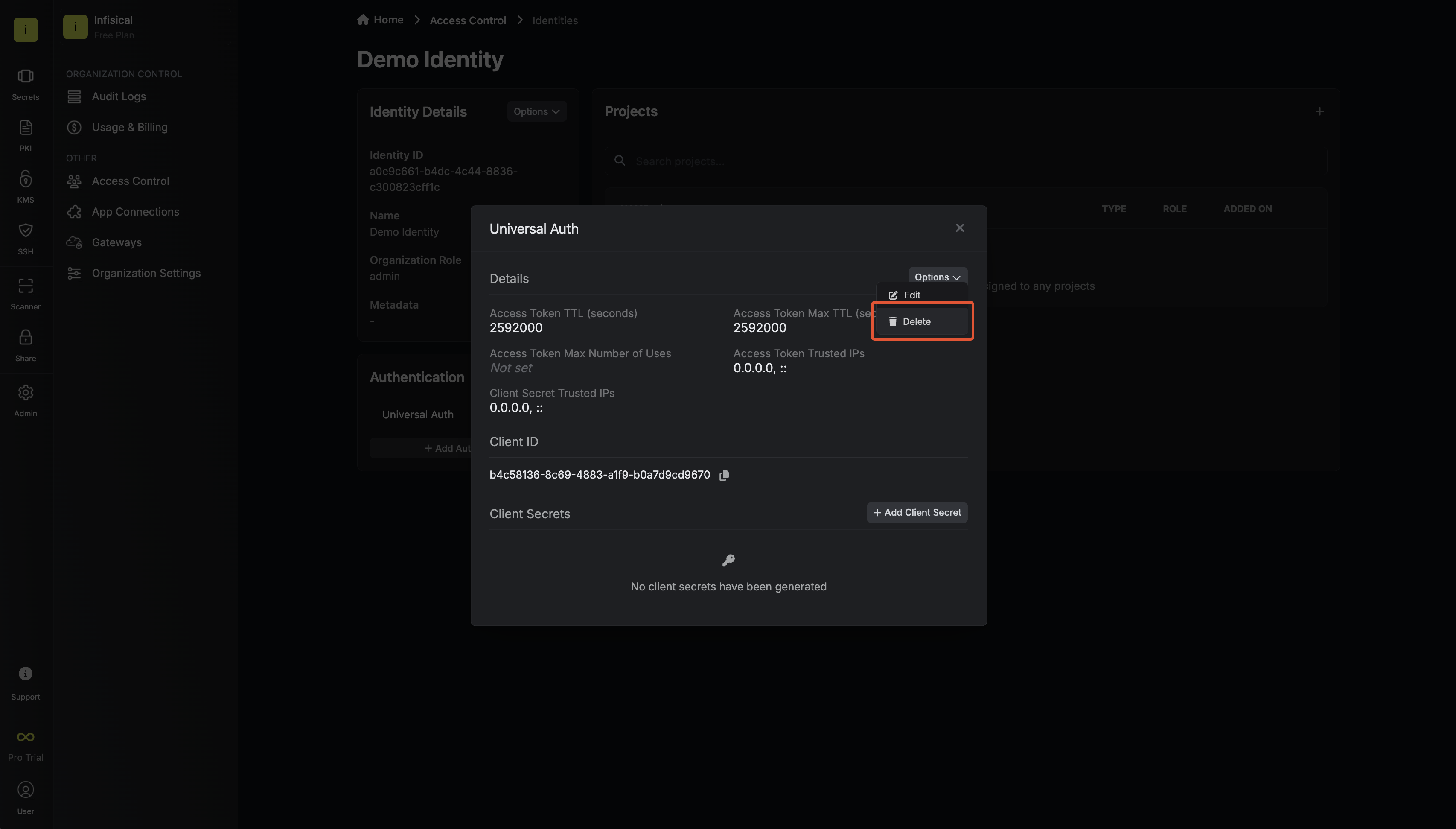
 Here’s some more guidance on each field:
Here’s some more guidance on each field:- Kubernetes Host / Base Kubernetes API URL: The host string, host:port pair, or URL to the base of the Kubernetes API server. This can usually be obtained by running
kubectl cluster-info. - Token Reviewer JWT: A long-lived service account JWT token for Infisical to access the TokenReview API to validate other service account JWT tokens submitted by applications/pods. This is the JWT token obtained from step 1.5(Reviewer Tab). If omitted, the client’s own JWT will be used instead, which requires the client to have the
system:auth-delegatorClusterRole binding. This is shown in step 1, option 2. - Allowed Service Account Names: A comma-separated list of trusted service account names that are allowed to authenticate with Infisical.
- Allowed Namespaces: A comma-separated list of trusted namespaces that service accounts must belong to authenticate with Infisical.
- Allowed Audience: An optional audience claim that the service account JWT token must have to authenticate with Infisical.
- CA Certificate: The PEM-encoded CA cert for the Kubernetes API server. This is used by the TLS client for secure communication with the Kubernetes API server.
- Access Token TTL (default is
2592000equivalent to 30 days): The lifetime for an acccess token in seconds. This value will be referenced at renewal time. - Access Token Max TTL (default is
2592000equivalent to 30 days): The maximum lifetime for an acccess token in seconds. This value will be referenced at renewal time. - Access Token Max Number of Uses (default is
0): The maximum number of times that an access token can be used; a value of0implies infinite number of uses. - Access Token Trusted IPs: The IPs or CIDR ranges that access tokens can be used from. By default, each token is given the
0.0.0.0/0, allowing usage from any network address.
Adding an identity to a project


Accessing the Infisical API with the identity
/var/run/secrets/kubernetes.io/serviceaccount/token path. This token should be used to authenticate with Infisical at the /api/v1/auth/kubernetes-auth/login endpoint.For information on how to configure sevice accounts for pods, refer to the guide here.We provide a code example below of how you might retrieve the JWT token and use it to authenticate with Infisical to gain access to the Infisical API.Sample code for inside an application
Sample code for inside an application
7200 seconds which can be adjusted.If an identity access token exceeds its max ttl, it can no longer authenticate with the Infisical API. In this case,
a new access token should be obtained by performing another login operation.Why is the Infisical API rejecting my service account JWT token?
Why is the Infisical API rejecting my service account JWT token?
- The Kubernetes Auth authentication method configuration is invalid.
- The service account JWT token has expired is malformed or invalid.
- The service account associated with the JWT token does not meet the criteria set forth in the Kubernetes Auth authentication method configuration such as Allowed Service Account Names and Allowed Namespaces.
Why is the Infisical API rejecting my access token?
Why is the Infisical API rejecting my access token?
- The access token has expired.
- The identity is insufficiently permissioned to interact with the resources you wish to access.
- The client access token is being used from an untrusted IP.
What is access token renewal and TTL/Max TTL?
What is access token renewal and TTL/Max TTL?

