Concept
Assuming that you’ve created a Private CA hierarchy with a root CA and an intermediate CA, you can now issue/revoke X.509 certificates using the intermediate CA.Workflow
The typical workflow for managing certificates consists of the following steps:- Issuing a certificate under an intermediate CA with details like name and validity period. As part of certificate issuance, you can either issue a certificate directly from a CA or do it via a certificate template.
- Managing certificate lifecycle events such as certificate renewal and revocation. As part of the certificate revocation flow, you can also query for a Certificate Revocation List CRL, a time-stamped, signed data structure issued by a CA containing a list of revoked certificates to check if a certificate has been revoked.
Note that this workflow can be executed via the Infisical UI or manually such
as via API.
Guide to Issuing Certificates
In the following steps, we explore how to issue a X.509 certificate under a CA.- Infisical UI
- API
1
Creating a certificate template
A certificate template is a set of policies for certificates issued under that template; each template is bound to a specific CA and can also be bound to a certificate collection for alerting such that any certificate issued under the template is automatically added to the collection.With certificate templates, you can specify, for example, that issued certificates must have a common name (CN) adhering to a specific format like  Here’s some guidance on each field:
Here’s some guidance on each field:
.*.acme.com or perhaps that the max TTL cannot be more than 1 year.Head to your Project > Certificate Authorities > Your Issuing CA and create a certificate template. Here’s some guidance on each field:
Here’s some guidance on each field:- Template Name: A name for the certificate template.
- Issuing CA: The Certificate Authority (CA) that will issue certificates based on this template.
- Certificate Collection (Optional): The certificate collection that certificates should be added to when issued under the template.
- Common Name (CN): A regular expression used to validate the common name in certificate requests.
- Alternative Names (SANs): A regular expression used to validate subject alternative names in certificate requests.
- TTL: The maximum Time-to-Live (TTL) for certificates issued using this template.
- Key Usage: The key usage constraint or default value for certificates issued using this template.
- Extended Key Usage: The extended key usage constraint or default value for certificates issued using this template.
2
Creating a certificate
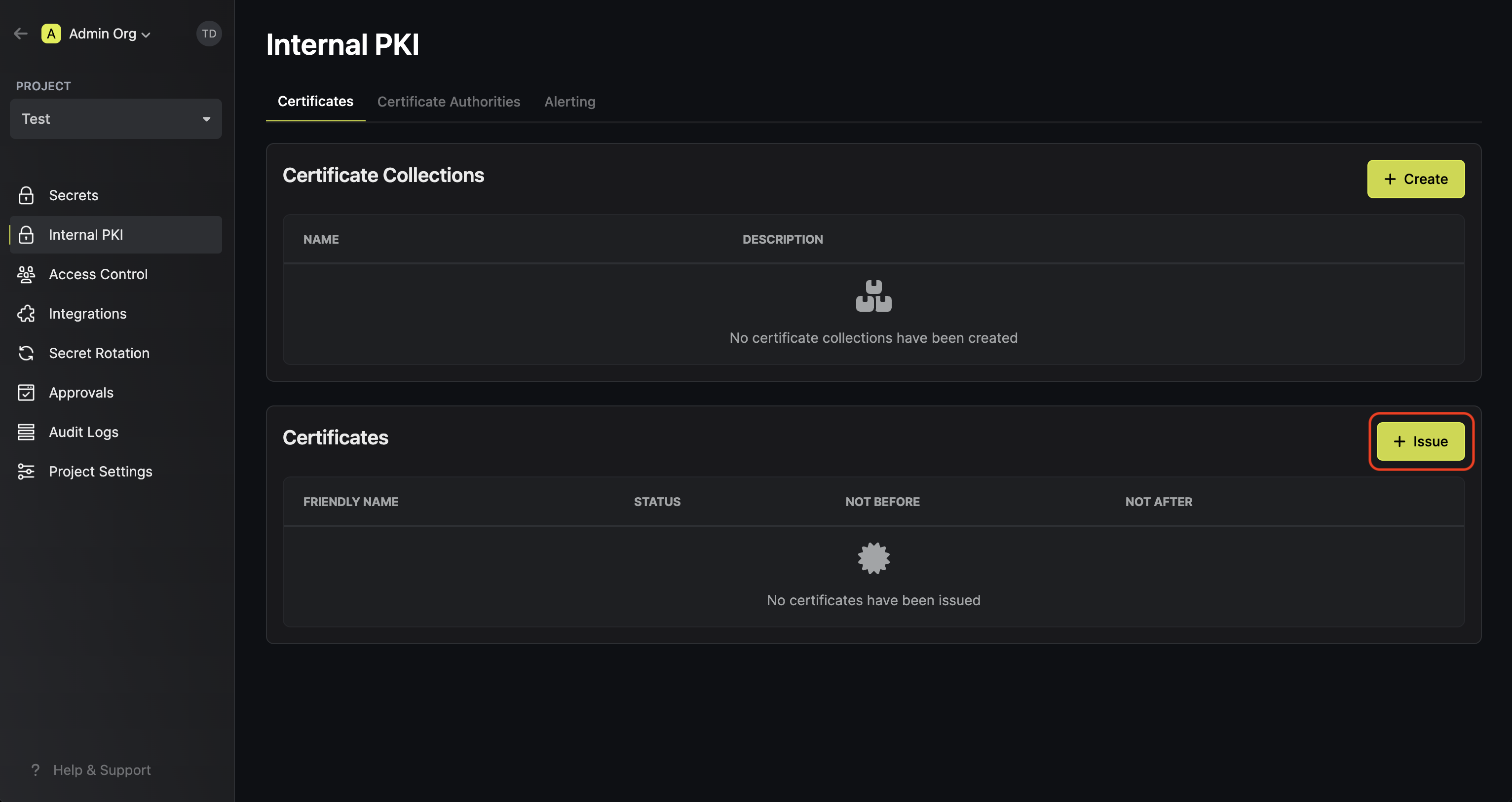
To create a certificate, head to your Project > Internal PKI > Certificates and press Issue under the Certificates section.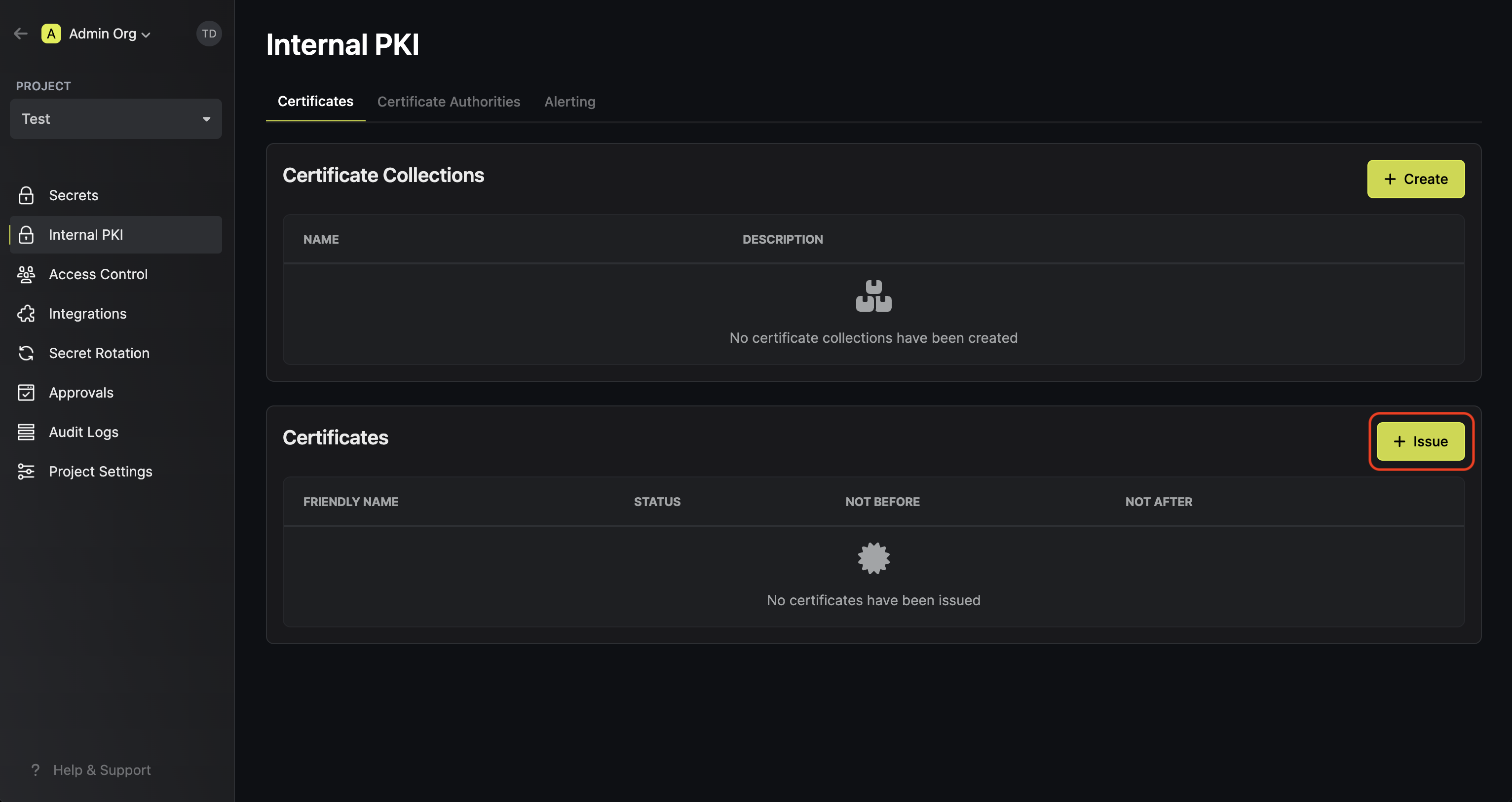 Here, set the Certificate Template to the template from step 1 and fill out the rest of the details for the certificate to be issued.
Here, set the Certificate Template to the template from step 1 and fill out the rest of the details for the certificate to be issued. Here’s some guidance on each field:
Here’s some guidance on each field:
 Here, set the Certificate Template to the template from step 1 and fill out the rest of the details for the certificate to be issued.
Here, set the Certificate Template to the template from step 1 and fill out the rest of the details for the certificate to be issued. Here’s some guidance on each field:
Here’s some guidance on each field:- Friendly Name: A friendly name for the certificate; this is only for display and defaults to the common name of the certificate if left empty.
- Common Name (CN): The common name for the certificate like
service.acme.com. - Alternative Names (SANs): A comma-delimited list of Subject Alternative Names (SANs) for the certificate; these can be hostnames or email addresses like
app1.acme.com, app2.acme.com. - TTL: The lifetime of the certificate in seconds.
- Key Usage: The key usage extension of the certificate.
- Extended Key Usage: The extended key usage extension of the certificate.
Note that Infisical PKI supports issuing certificates without certificate templates as well. If this is desired, then you can set the Certificate Template field to None
and specify the Issuing CA and optional Certificate Collection fields; the rest of the fields for the issued certificate remain the same.That said, we recommend using certificate templates to enforce policies and attach expiration monitoring on issued certificates.
3
Copying the certificate details
Once you have created the certificate from step 1, you’ll be presented with the certificate details including the Certificate Body, Certificate Chain, and Private Key.

Make sure to download and store the Private Key in a secure location as it will only be displayed once at the time of certificate issuance.
The Certificate Body and Certificate Chain will remain accessible and can be copied at any time.
Guide to Revoking Certificates
In the following steps, we explore how to revoke a X.509 certificate under a CA and obtain a Certificate Revocation List (CRL) for a CA.- Infisical UI
- API
1
Revoking a Certificate
Assuming that you’ve issued a certificate under a CA, you can revoke it by
selecting the Revoke Certificate option for it and specifying the reason
for revocation.



2
Obtaining a CRL
In order to check the revocation status of a certificate, you can check it
against the CRL of a CA by heading to its Issuing CA and downloading the CRL. To verify a certificate against the
downloaded CRL with OpenSSL, you can use the following command:Note that you can also obtain the CRL from the certificate itself by
referencing the CRL distribution point extension on the certificate.To check a certificate against the CRL distribution point specified within it with OpenSSL, you can use the following command:
To verify a certificate against the
downloaded CRL with OpenSSL, you can use the following command:Note that you can also obtain the CRL from the certificate itself by
referencing the CRL distribution point extension on the certificate.To check a certificate against the CRL distribution point specified within it with OpenSSL, you can use the following command:
 To verify a certificate against the
downloaded CRL with OpenSSL, you can use the following command:
To verify a certificate against the
downloaded CRL with OpenSSL, you can use the following command:FAQ
What is the workflow for renewing a certificate?
What is the workflow for renewing a certificate?
To renew a certificate, you have to issue a new certificate from the same CA
with the same common name as the old certificate. The original certificate
will continue to be valid through its original TTL unless explicitly
revoked.

