Infisical’s Azure Entra ID Connection lets you authenticate with Microsoft Entra ID (formerly Azure Active Directory) using Client Secrets. Prerequisites:Documentation Index
Fetch the complete documentation index at: https://infisical.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
- Set up an Azure account with an existing Azure Entra ID tenant.
- Register an App Registration in Azure with the necessary Microsoft Graph API permissions for your use case.
Required Azure Permissions
Required Azure Permissions
The permissions required for your Azure Entra ID Connection depend on what you intend to use it for.For SCIM Token Secret Sync:Your App Registration must have the following Microsoft Graph API Application permissions:
-
Application.ReadWrite.All— Required to read and update synchronization secrets (SCIM tokens) on enterprise application service principals. -
Synchronization.ReadWrite.All— Required to list synchronization jobs on service principals and to write SCIM provisioning tokens.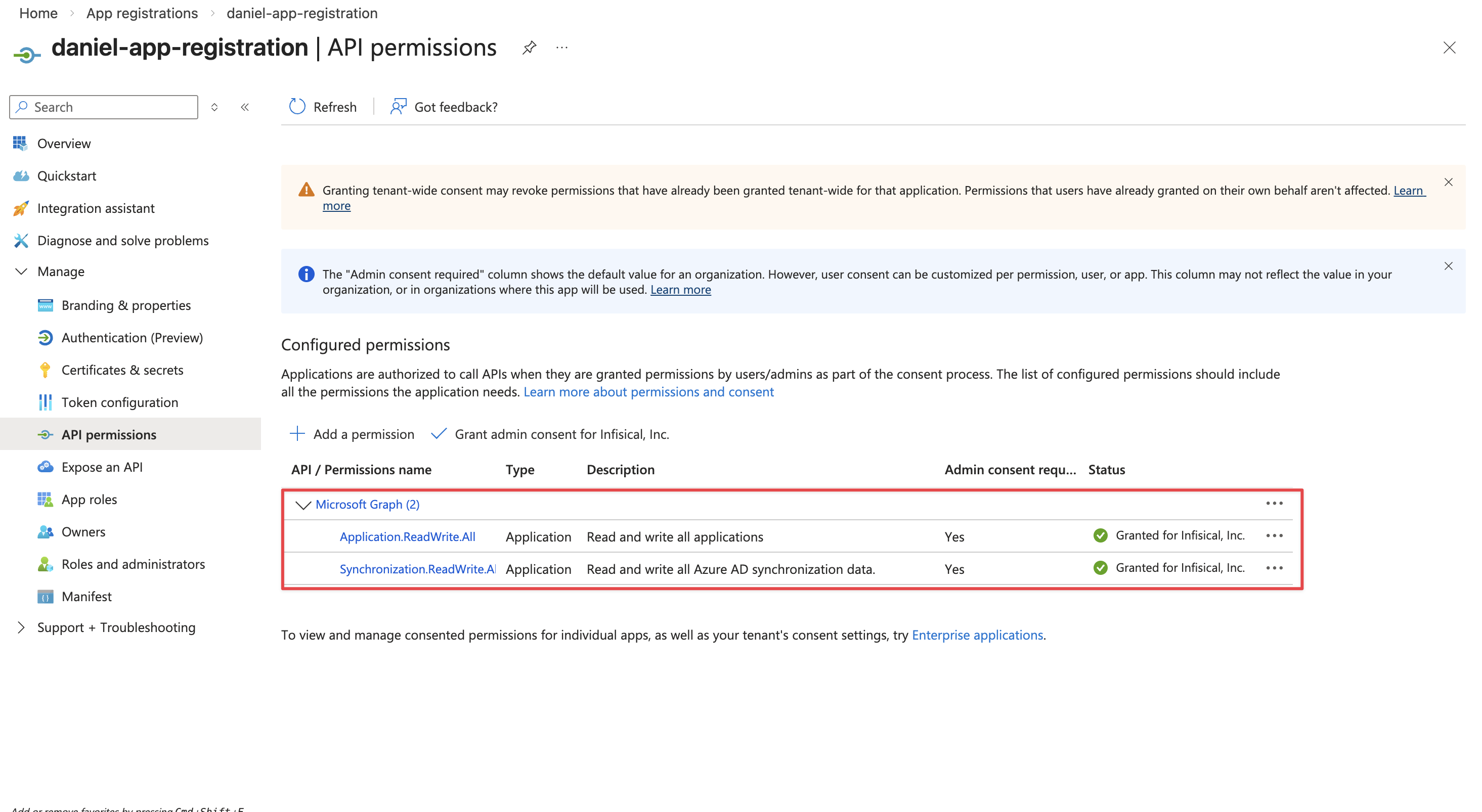
After adding the permission, an admin must Grant admin consent for the permission to take effect.
Setup Azure Entra ID Connection in Infisical
- Infisical UI
- API
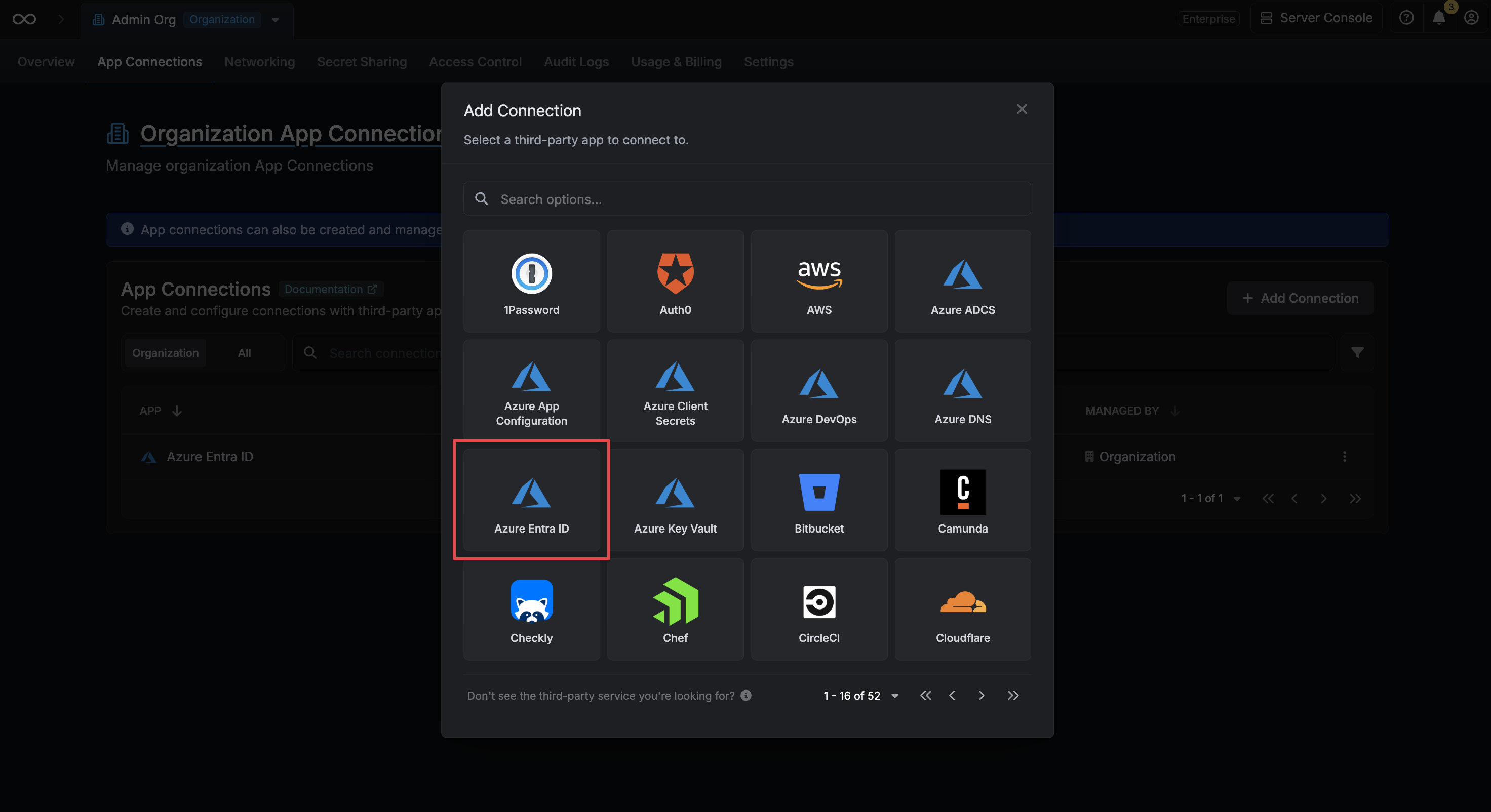
Navigate to App Connections
Navigate to the Organization Settings page, then select App Connections. Click on the Add Connection button.

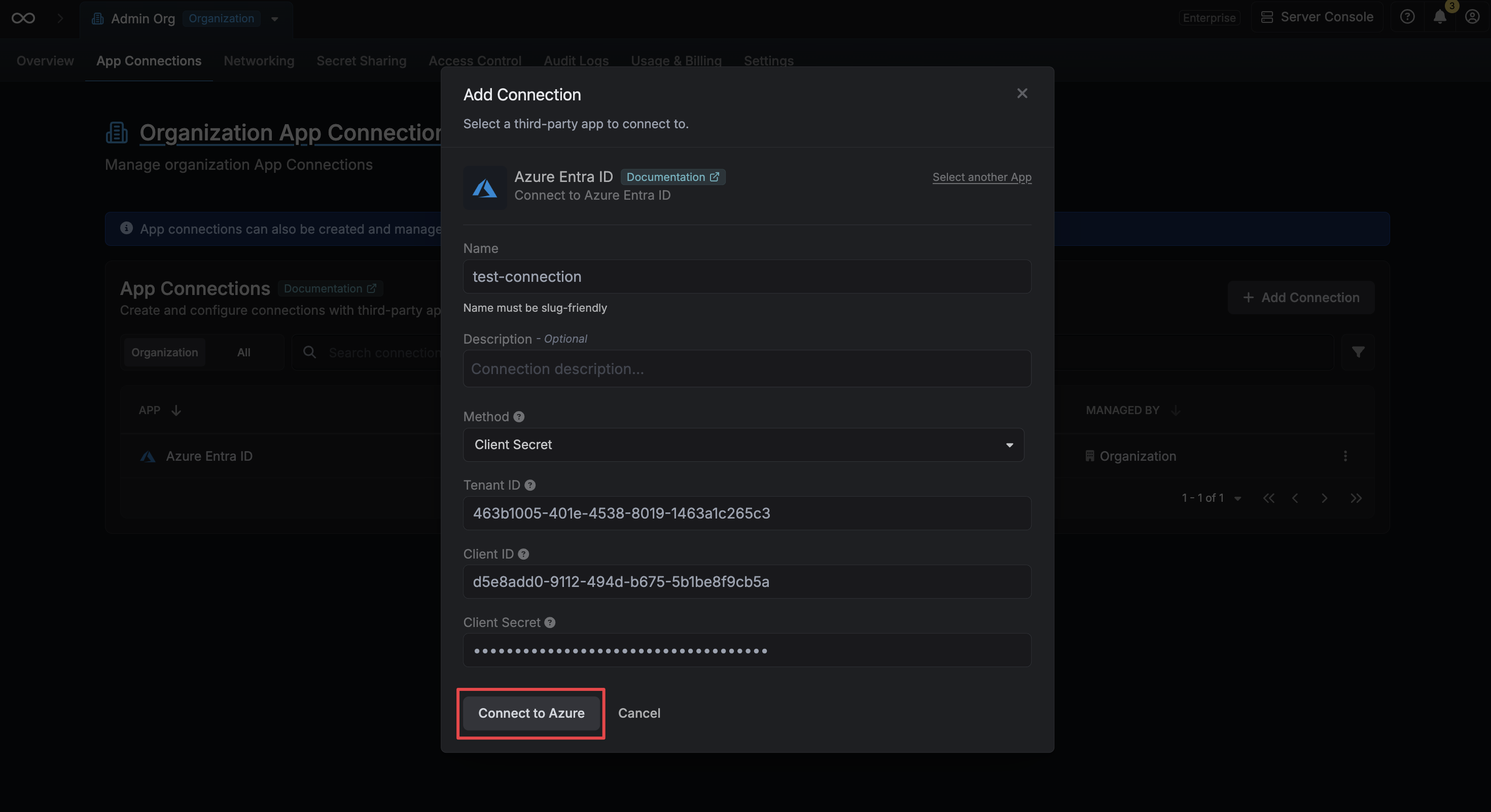
Create Connection
Fill in the following fields with the credentials from your Azure App Registration: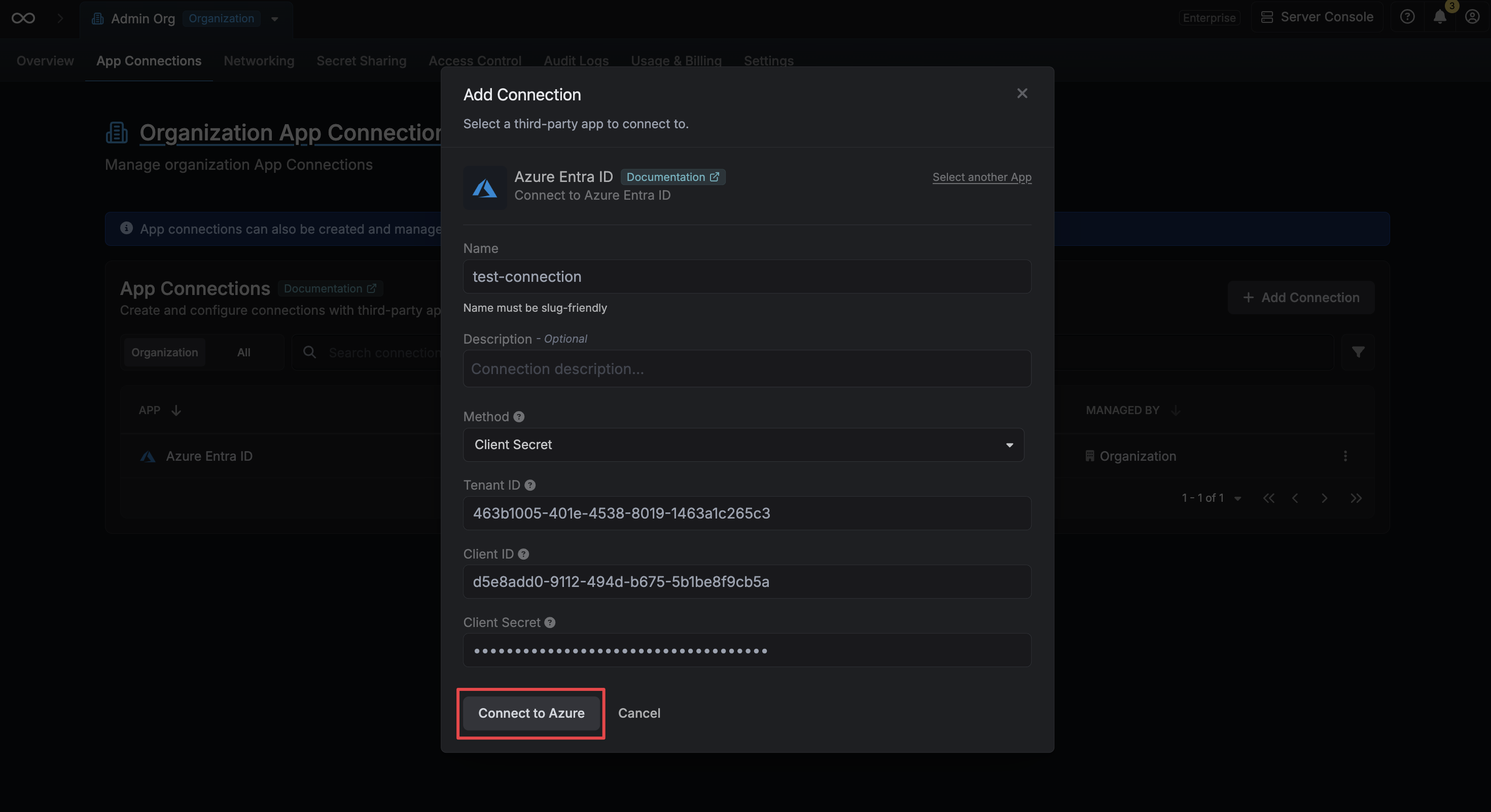
- Tenant ID: The Directory (Tenant) ID of your Azure Entra ID tenant.
- Client ID: The Application (Client) ID of your registered application.
- Client Secret: A client secret generated for your registered application.